Relying on a cloud provider like AWS, Microsoft Azure, or Google Cloud is now standard practice for many companies. But almost always taken for granted is the security offered by these platforms. The problem? Basic protection doesn’t cover everything, leaving critical points exposed that can put your data and infrastructure at real risk. In 2026, cybersecurity in cloud environments requires much more than antivirus, firewalls, and automatic logs. A customized, proactive, and compliance-ready approach is needed to detect threats in [...]
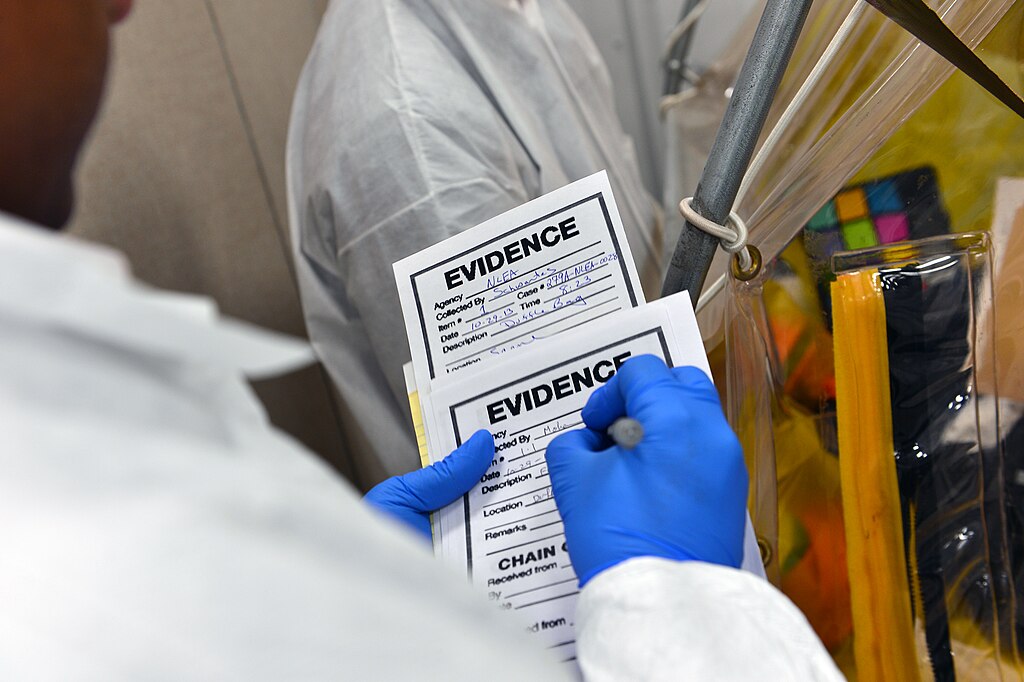
In the contexts of Digital Forensics and Cybersecurity in general, it has been discussed for many years… yet, when it comes to practice, the reality is different: in most organizations, the chain of custody does not exist or is not applied correctly. In some cases because it is unknown, in others because it is seen as a mere bureaucratic formality: a document to be filled out only by “those who really need it”. The consequences? Internal digital investigations lacking [...]