In the contexts of Digital Forensics and Cybersecurity in general, it has been discussed for many years… yet, when it comes to practice, the reality is different: in most organizations, the chain of custody does not exist or is not applied correctly.
In some cases because it is unknown, in others because it is seen as a mere bureaucratic formality: a document to be filled out only by “those who really need it”. The consequences? Internal digital investigations lacking a solid documentary foundation. Disciplinary decisions that become more fragile in the face of a challenge. Digital evidence that risks losing all value.
The Chain of Custody, on the other hand, is designed precisely to protect the actions of those conducting legitimate and correct investigations.
What is the Chain of Custody
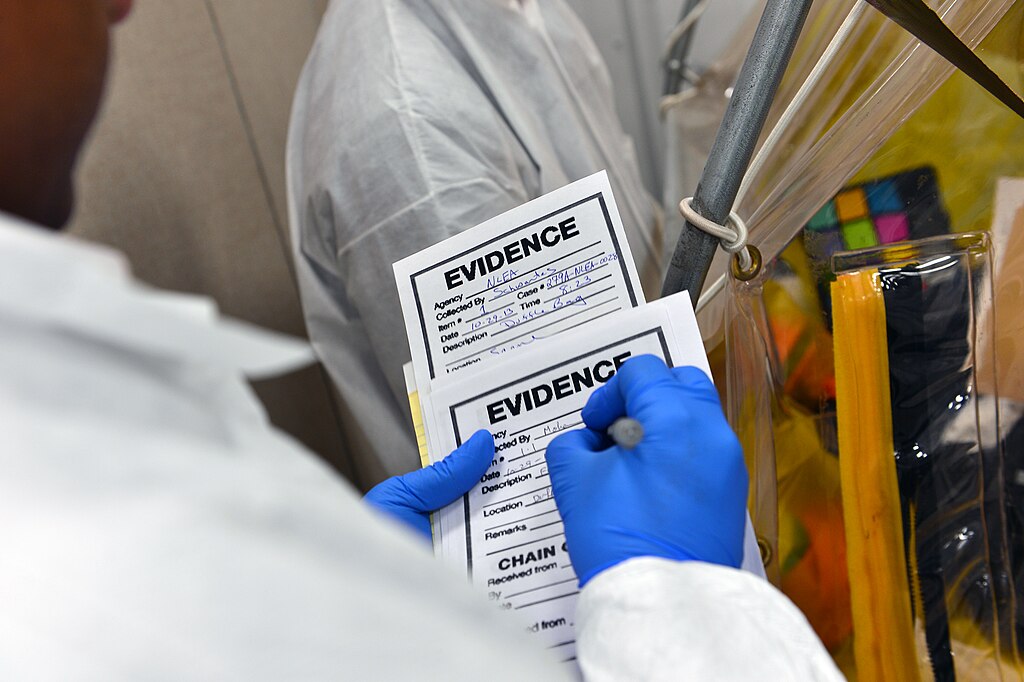
The term comes from the forensic world and refers to the set of activities that allow for traceable documentation of the management of evidence:
- who collected it
- where it was stored
- who accessed it
- for what reason
The concept does not only concern physical evidence, but also naturally digital evidence, which today represents the majority of relevant information sources: email, corporate documents, internal messaging, system access, logs, content on corporate devices.
Digital evidence lacking an adequate chain of custody risks being considered unreliable, because it is not possible to guarantee that it has not been altered.
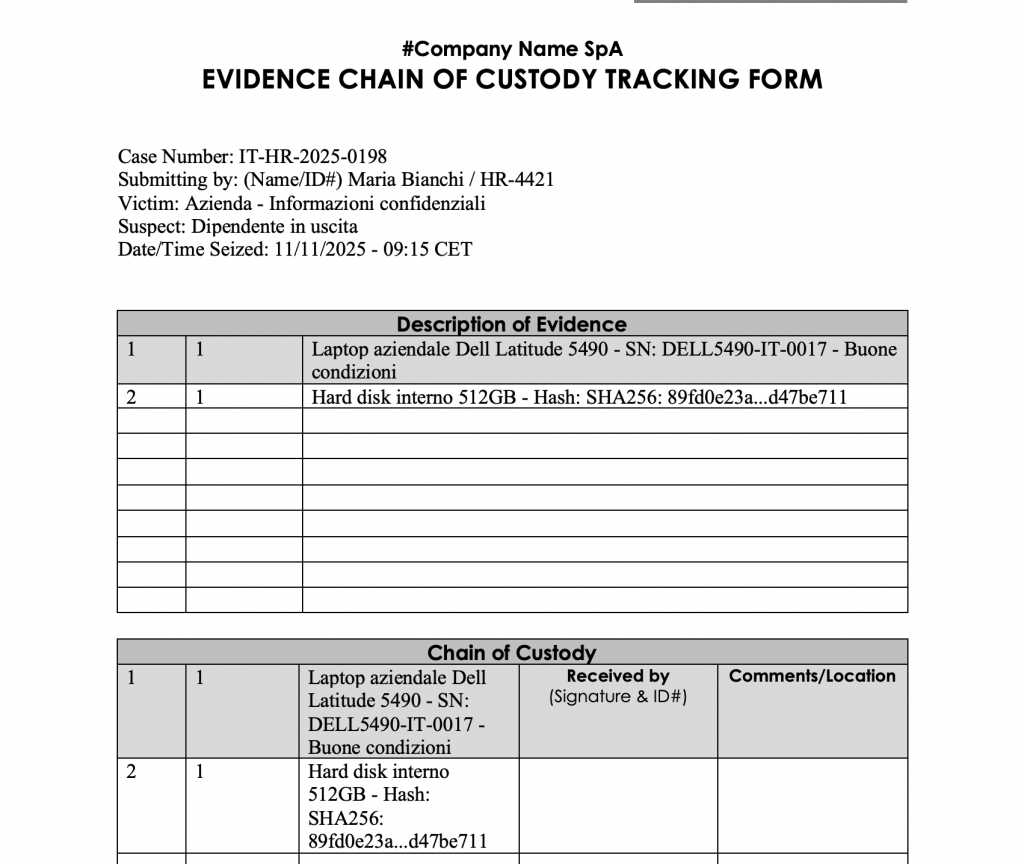
https://www.nist.gov/document/sample-chain-custody-formdocx
Why it is also crucial for a company
The management of digital evidence in the context of an HR investigation has not only technical value. It protects the credibility of the process, safeguards the rights of the individuals involved, and reduces the risk of disputes. In the event of litigation or involvement of judicial authorities, the ability to demonstrate data integrity becomes a decisive factor.
Even when the forensic computer investigation remains internal, adopting transparent and verifiable procedures means operating with professionalism and responsibility.
The fundamental elements of proper management
An adequate Chain of Custody is based on several essential principles:
- clear and detailed identification of the evidence from the moment of collection;
- complete recording of every transfer or activity involving the evidence;
- storage in controlled environments, physical or digital, with limited and monitored access;
- traceability of the analyses conducted, the tools used, and the conclusions reached;
- definition of the closure moment, with documented archiving, return, or destruction.
These steps allow us to assert with rigorous certainty that the digital evidence is authentic and reliable.
The consequences of inadequate management
If the chain of custody is not respected, the solidity of the entire investigative framework can be compromised. Disciplinary decisions become more vulnerable to appeals, the company is exposed to legal and economic risks, and trust in internal processes is undermined.
The Chain of Custody thus represents a concrete safeguard for the protection of all parties involved.
A structured approach at the service of corporate culture
Systematizing these practices means strengthening the organizational maturity of the company, promoting more transparent and well-founded investigative processes. The Chain of Custody is not just a technical measure, but a cultural element that involves ethics, governance and protection of individuals.
To learn more
Our experience has led us to support various organizations in defining internal procedures for managing digital evidence, facilitating collaboration between HR, Legal, IT, and Compliance. Knowing and correctly applying the Chain of Custody means being prepared to effectively manage critical and delicate situations.